Prioritizing CWE/SANS and OWASP Vulnerabilities: A Network-Based Model. - Document - Gale Academic OneFile

Amazon.com: SCFM: Secure Coding Field Manual: A Programmer's Guide to OWASP Top 10 and CWE/SANS Top 25 eBook : Wear, Natalie "Sunny": Kindle Store
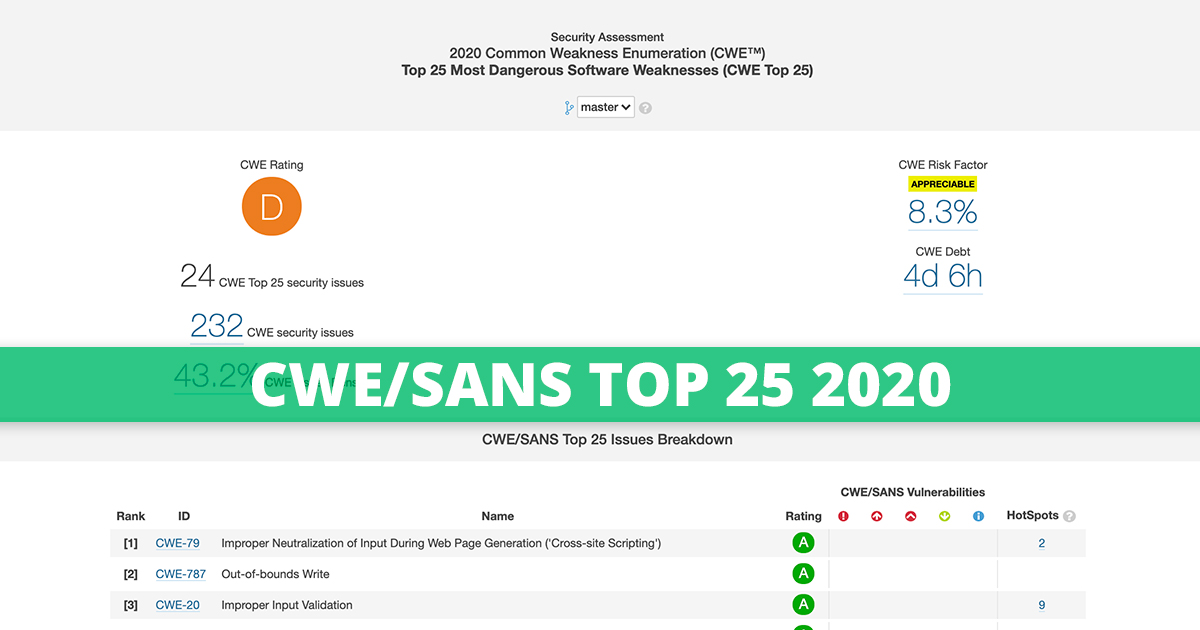
GitHub - gokulakannant/Top-10-Web-Application-Vulnerabilities: The SANS Top 25 Software errors mapped to Top 10 OWASP vulnerabilities in 2020.
PDF) Vulnerabilities Mapping based on OWASP-SANS: A Survey for Static Application Security Testing (SAST)

SANS Top 25 Most Dangerous Programming Errors Catagory 1: Insecure Interaction Between Components These weaknesses are related to insecure ways. - ppt download